[ad_1]
How this malware can affect users
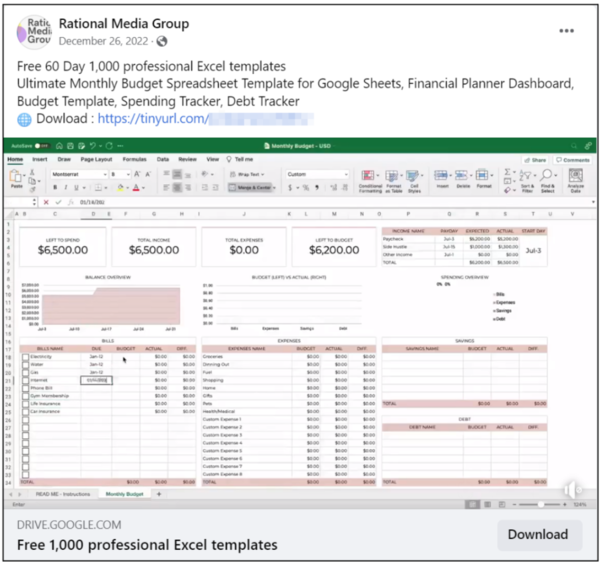
In December 2022, a phishing campaign was used for delivering two variants of malware. The attacker used multiple Facebook pages and users to post information luring victims to download a link from known cloud file storage providers. After clicking, a .zip file was downloaded, containing the malicious infostealer .exe files. The report has also shared an example of the Facebook phishing post luring victims to download the infected .zip file.
The first variant creates various processes that could be considered abnormal activity indicators, including shutting pop-up windows on the graphical user interface (GUI). Meanwhile, the second variant is more discrete making it tougher to identify malicious activity.
Both variants can steal Facebook business account credentials by connecting to the Meta Graph API with the victim’s user ID and access token. The Graph API is the primary way to get data in and out of Facebook and can be used to programmatically query data, post, manage ads and more.
It is used to steal information about the target’s follower count, user verification status, whether the account is prepaid and send it to the command and control server (C2). They also attempt to steal the login credentials by checking the cookies and local databases of the most common browsers.
In comparison, the second variant goes one step further by replacing the legitimate user’s email address with a mailbox under the cyberattacker’s control, thereby locking them out of the account indefinitely.
[ad_2]
Source link










More Stories
Google Maps: Three privacy features coming to Google Maps on Android, iPhones
Most-Downloaded IPhone App: This Chinese app was the most-downloaded iPhone app in the US in 2023
Ukraine’s largest mobile operator goes offline for millions of users after cyber attack